Cyberattacks are taking place all the time; even now the security of some organizations big or small is at constant threat. Almost every other day you will hear the news of an unauthorized attacker stealing the data from websites. Magento has had its share of attacks and vulnerabilities too.
A possible hack on your website does not only affect you & your business but at the same time affects your customers too. If you own an eCommerce website on the Magento platform, you need to know all about the Magento security threats.
Do you want to secure your website from a possible threat? If yes, then you are at the right place; this blog post covers everything you need to know about threats of Magento security.
What is Magento?
Magento is one of the most favored choices for an e-commerce platform with over 170,282 websites to its name. It is written in PHP and offers versatile features to its customers. The popularity of Magento can also be attributed to it being an open-source platform, which provides room for customization.
Magento comes in two editions; community edition which is free for all and enterprise edition which is a premium version. In spite of listed in the popular eCommerce platforms, Magento has suffered its fair share of attacks as well.
Magento Security Threats Making You Vulnerable
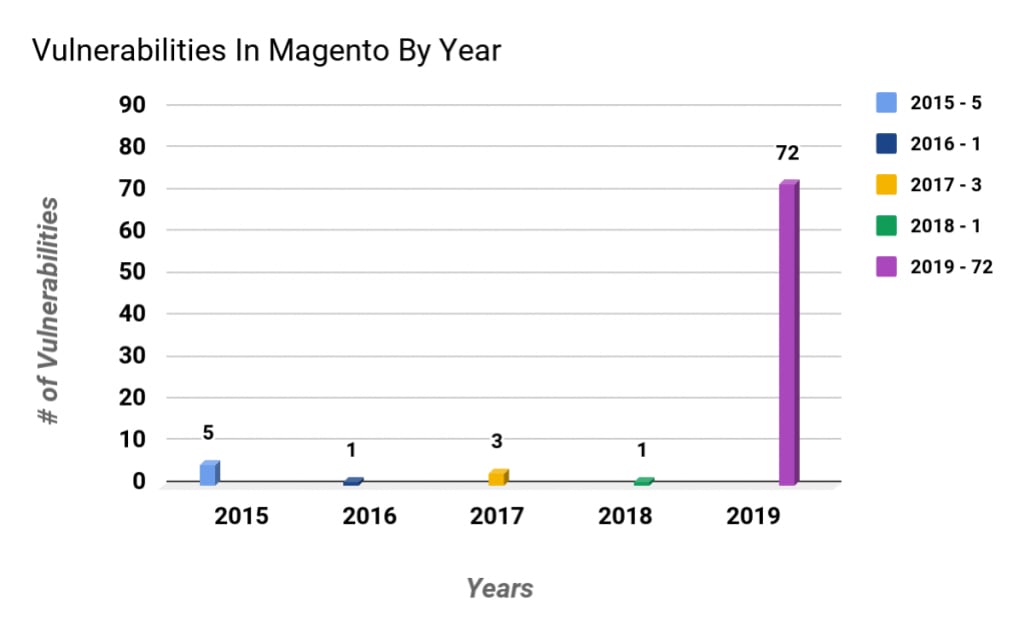
In the next section, I will give you a closer look into the Magento security threats that the stores face currently. Here is a sample of how many vulnerabilities Magento receives per year.
Suggested Read: Home Security Guidelines Which You Have Not Thought Of
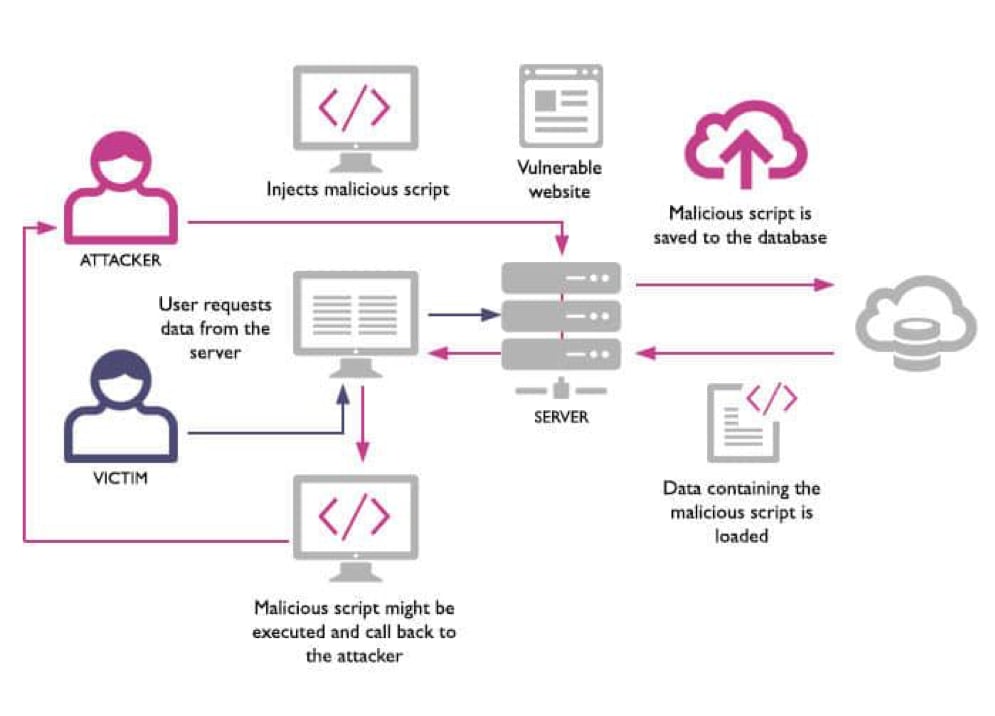
Cross-site Scripting(XSS)
It is a client-side code injection attack. It allows the injection of malicious code into a website.
Mainly the ability of an attacker is to run arbitrary scripts on the website that is used later on to track what orders people are buying and manipulate them to change their shipping address.
Possible causes:
- It may be because of your website fame.
- Another possible cause could be some ad on another website that can affect your website.
- It could also be due to some bad tracking tool you used.
Preventing XSS attack:
- Input Validation, The obvious way to prevent cross-site scripting attacks by limiting the allowable user inputs. You can do this by blacklisting certain characters from being used.
- Input Transformation, Encoding; changing input so that it cannot be interpreted as code.
- Escaping, handling special characters properly by preventing them from being parsed as code.
- Sanitizing user input describes cleansing user input to prevent it from jumping the fence and exploiting security loopholes.
For further information, you can click here.
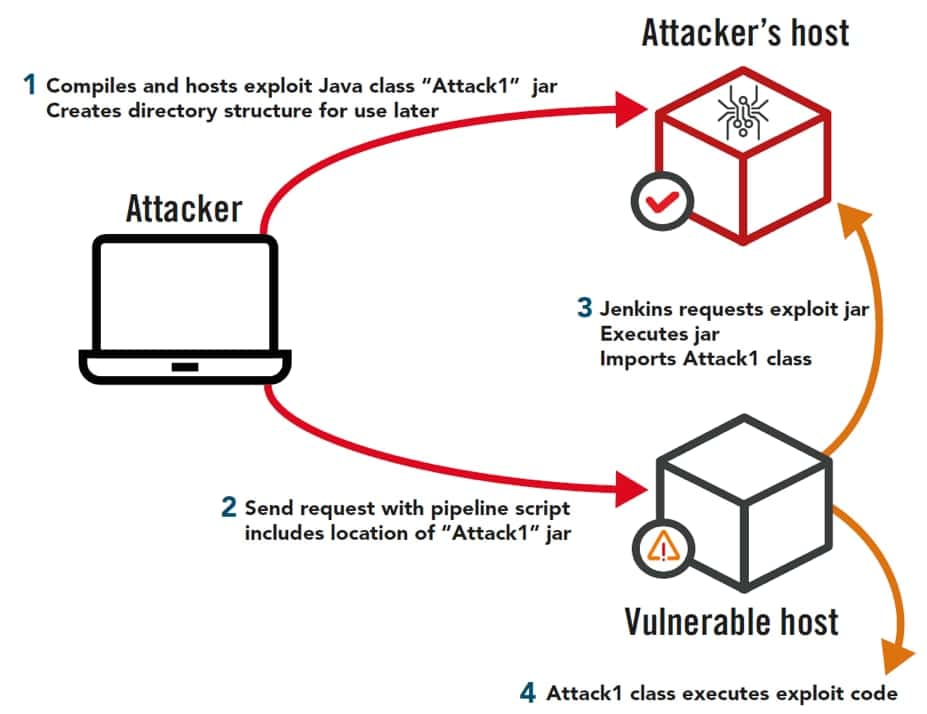
Remote Code Execution
What an attacker would do to completely compromise a system is what refers to as remote code execution. It is also known as arbitrary code execution because the attacker executes arbitrary code on the compromised system.
By the use of these arbitrary codes, the attacker takes complete control of the system. The attacker can exploit the root/admin privileges via code execution.
It is not necessary that on accessing the system the attacker will get access to root/admin privileges but it is highly probable.
Possible Causes:
- Opening spam can lead you to a phishing link.
- Visiting a hacked website etc.
Preventing Remote code execution attack:
- Keeping your system up to date with the latest software,i.e; always install the latest version of Magento.
- Make sure that your code knows the limits of your data buffers.
- Always assume that you are under a constant threat.
Suggested Read: Best Home Security Cameras To Protect Your Home
Injection Vulnerabilities
In an Injection attack, an attacker supplies or injects untrusted and harmful input to a program. These inputs are often interpreted as a command or sometimes as query and alter the whole execution of the program.
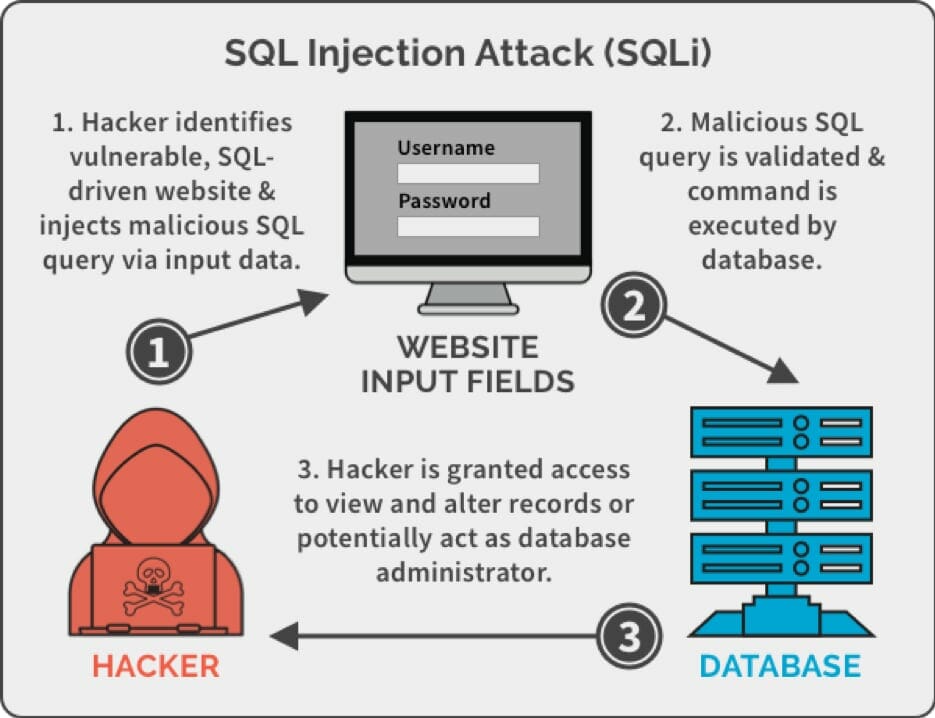
SQL injection is the most dangerous and widespread type of injection. To exploit a SQL injection vulnerability, the intruder needs to find a variable that the application passes through a database. By embedding bad SQL commands into the content of the variable, the intruder tricks the application into spreading a bad query in the database.
Preventing Injection attack:
- Using Parameterized Queries, In this method, the SQL code is defined first. This will help in distinguishing between code and data, regardless of the input.
- Use Stored Procedures, It almost has the same effect as that of parameterized queries.
- Escaping all User Supplied Input, When nothing works this method can be helpful. This technique escapes the user before using it in a query.
For further information, visit How to secure the Magento store from the SQL injection attack.
Suggested Read: Best Smart Door Locks To Prevent Theft At Your Home
CSRF (Cross-Site Request Forgery) Attack
In this attack, the user is tricked into doing some unwanted task. This may cause a loss of trust between the website and its user. As the attacker cannot see what the user is responding to the malicious requests, so this attack focuses on the change of state rather than focusing on data theft.
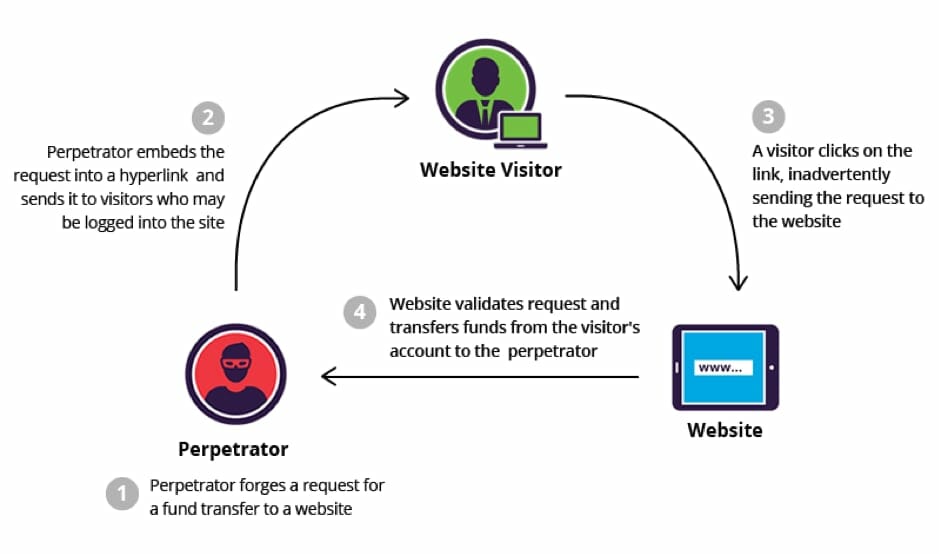
Magento’s GiftCard Account removal feature was found at risk to a Cross-site request forgery attack in the year 2019.
Preventing CSRF attack:
- Synchronizer Token Pattern, In this technique a unique token is generated. When the user does some unwanted work, Synchronizer Token Pattern searches for the unique token attached to a user session.
- Cookie-to-header Token, In this technique the token generated in the cookie which is in association with the user session.
- Double submit cookie, Same as before, but instead of using JAVASCRIPT, the token is well hidden in the HTML field.
- Same site cookie attribute, This mechanism makes sure that the cookie will only be accessed by the site it was set by.
Not Demanding Security Audit
Network security audits are vital because they assist you identify your biggest security risks so you’ll make changes that will protect your company from those risks. That’s pretty common knowledge. … You are going to require running such audits a minimum of once a year (if less frequently).
Suggested Read: How To Secure Your WordPress site With Security Ninja
Neglecting Sub-Domains on the Same Domain
These subdomains can be sometimes abused by the attackers to get persistent cross-site scripting. Subdomain infringement is an unsuspected threat that is going undetected by the respective security team.
Misconfigured API Access Permissions
Anyone can request API information and by doing so can get the information about your products. But in many cases, it is possible that if a person knows API he/she can extract any other important information from your website and can manipulate them.
Even if the worst happens and you get attacked, here are few steps which can help you recover.
- Use a backup.
- Call law enforcement.
- Do a full wipe of system.
- Reinstall the Magento.
- Double-check your admin accounts.
- Change passwords assuming everything is compromised.
- Be transparent towards your customers.
So these are some of the security threats for Magento which you should be aware of and take precaution.